How To Install GLPI on Fedora 43

If your team is drowning in spreadsheets trying to track hardware, tickets, and software licenses, GLPI (Gestionnaire Libre de Parc Informatique) solves that problem with a single open-source platform. This Linux server tutorial walks you through every step to install GLPI on Fedora 43, from installing the LAMP stack to running the final setup wizard. By the end, you will have a fully working, secured GLPI instance that your team can log into and start using. Whether you are configuring GLPI on Fedora 43 for a small office or a large enterprise network, this guide gives you the exact commands and explanations you need.
What Is GLPI and Why Run It on Fedora 43
GLPI is a free, open-source IT service management (ITSM) platform built to help sysadmins manage assets, users, helpdesk tickets, software licenses, and contracts from one centralized web interface. It is ITIL-compliant, actively maintained, and used by thousands of organizations worldwide.
Fedora 43 is a strong host for GLPI because of its modern DNF package manager, tight SELinux integration out of the box, and fast access to community repositories like Copr. It runs the same RPM-based stack as RHEL and CentOS, so most enterprise deployment patterns carry over cleanly.
Core Features of GLPI
- Hardware inventory management for computers, printers, and network devices
- Incident, request, problem, and change management (ITIL-aligned)
- Software license and warranty tracking
- Data Center Infrastructure Management (DCIM)
- Asset reservation and contract management
- Built-in knowledge base and FAQ system
Prerequisites
Before you run a single command, make sure your environment meets these requirements.
Hardware Requirements
- RAM: 2 GB minimum; 4 GB or more for any real production load
- Disk: At least 20 GB free to cover the OS, GLPI files, and database growth
- CPU: Any modern 64-bit processor works fine for a standard GLPI deployment
Software Requirements
- A clean Fedora 43 installation (physical server, VM, or VPS)
- A user account with sudo access
- PHP 8.1 or higher with extensions:
json,mbstring,mysqli,gd,curl,session - MariaDB 10.6 or higher as the database backend
- Apache 2.4 as the web server
- Optional but recommended:
php-imapfor email collection,php-ldapfor Active Directory integration
Network Requirements
- Port 80 (HTTP) and port 443 (HTTPS) accessible on your firewall
- A hostname or IP address pointed at the server
- Internet access on the server to download packages
Step 1: Update the System and Set the Timezone
Always start a fresh installation with a full system update. This pulls in the latest security patches and ensures package compatibility throughout the rest of the setup.
sudo dnf update -yNext, set your system timezone. GLPI uses the server timezone for log entries, scheduled jobs, and ticket timestamps. A wrong timezone causes confusing gaps in your audit trail.
sudo timedatectl set-timezone America/New_YorkReplace America/New_York with your actual timezone. You can list all available timezones with timedatectl list-timezones.
Verify the timezone applied correctly:
timedatectl statusYou should see your selected timezone listed under Time zone.
Step 2: Configure the Firewall and SELinux
Fedora 43 runs firewalld and SELinux in enforcing mode by default. You need to configure both before Apache can serve GLPI traffic.
Open HTTP and HTTPS Ports
sudo firewall-cmd --permanent --add-service=http
sudo firewall-cmd --permanent --add-service=https
sudo firewall-cmd --reloadThe --permanent flag makes these rules survive reboots. The --reload applies them immediately without restarting the firewall service.
Set SELinux Booleans for Apache
SELinux controls what processes can communicate with each other. Apache needs three specific booleans enabled to let GLPI work properly:
sudo setsebool -P httpd_can_network_connect on
sudo setsebool -P httpd_can_network_connect_db on
sudo setsebool -P httpd_can_sendmail onHere is what each boolean does:
httpd_can_network_connect: Allows Apache to make outbound network connections, needed for GLPI plugins and external integrationshttpd_can_network_connect_db: Allows Apache to connect to the MariaDB databasehttpd_can_sendmail: Allows Apache to send email notifications through GLPI’s mail system
The -P flag makes each change persistent across reboots.
Step 3: Install and Configure MariaDB
MariaDB is the recommended database server for GLPI. It delivers excellent performance, full utf8mb4 character set support, and solid compatibility with all GLPI versions.
Install MariaDB
sudo dnf install mariadb-server -y
sudo systemctl enable mariadb
sudo systemctl start mariadbConfirm it is running:
sudo systemctl status mariadbYou should see active (running) in the output.
Secure the MariaDB Installation
Run the built-in security script to lock down defaults:
sudo mysql_secure_installationWork through each prompt:
- Set a strong root password when asked
- Remove anonymous users: Yes
- Disallow remote root login: Yes
- Remove the test database: Yes
- Reload privilege tables: Yes
Create the GLPI Database and User
Log into MariaDB as root:
sudo mysql -u root -pInside the MariaDB shell, run these commands:
CREATE DATABASE glpidb CHARACTER SET utf8mb4 COLLATE utf8mb4_unicode_ci;
CREATE USER 'glpiuser'@'localhost' IDENTIFIED BY 'YourSecurePassword123!';
GRANT ALL PRIVILEGES ON glpidb.* TO 'glpiuser'@'localhost';
FLUSH PRIVILEGES;
EXIT;The utf8mb4 character set handles the full Unicode range, including multi-byte characters used in non-Latin languages. Plain utf8 in MySQL/MariaDB is actually a 3-byte subset and breaks on some characters. GLPI’s international user base makes utf8mb4 the correct choice.
Verify the connection works before moving forward:
mysql -u glpiuser -p -h localhost glpidbA successful login confirms the database and user are ready.
Step 4: Install Apache HTTP Server
Apache handles all incoming web requests for GLPI. Install it, enable it at boot, and start it in one sequence:
sudo dnf install httpd -y
sudo systemctl enable httpd
sudo systemctl start httpdCheck that Apache is running:
sudo systemctl status httpdYou should see active (running). If you open a browser and navigate to your server’s IP address, the default Fedora Apache test page should load. That confirms Apache is serving traffic correctly.
mod_rewrite is already bundled with Fedora’s Apache package, so you do not need to install it separately. GLPI’s URL routing depends on it.
Step 5: Install PHP and Required Extensions
GLPI requires PHP 8.1 or higher with a specific set of extensions. Install them all in one command to avoid missing dependencies later:
sudo dnf install php php-gd php-mysqlnd php-ldap php-mbstring php-intl \
php-xml php-xmlrpc php-curl php-json php-imap php-zip php-opcache php-apcu -yTune PHP for GLPI
Open the main PHP configuration file:
sudo nano /etc/php.iniFind and update these values:
memory_limit = 256M
max_execution_time = 300
upload_max_filesize = 32M
post_max_size = 32M
session.cookie_httponly = On
date.timezone = America/New_YorkHere is why each setting matters:
memory_limit = 256M: Prevents out-of-memory crashes when GLPI processes large inventory scansmax_execution_time = 300: Gives GLPI enough time to complete long-running database operationsupload_max_filesize = 32M: Allows users to attach reasonably sized files to ticketssession.cookie_httponly = On: Blocks JavaScript from reading session cookies, a basic XSS defensedate.timezone: Must match the timezone you set in Step 1
Restart Apache to load the new PHP settings:
sudo systemctl restart httpdStep 6: Install GLPI on Fedora 43
You have two solid options here. The Copr repository method is faster and easier to maintain. The manual method gives you precise version control.
Method 1: Copr Repository (Recommended)
Enable the community Copr repository maintained for enterprise GLPI deployments on Fedora:
sudo dnf copr enable ligenix/enterprise-glpi10 -y
sudo dnf update -yInstall GLPI along with all required dependencies in a single command:
sudo dnf install mariadb-server httpd php-fpm glpi -yVerify the installation completed successfully:
rpm -qi glpiThe output displays the GLPI version, installation date, and build details. This method automatically sets correct file permissions and SELinux contexts, which saves you several manual steps.
Method 2: Manual Installation from Source
This approach suits development environments or cases where you need a specific GLPI version not available through Copr.
Download the latest GLPI release and its signature file:
cd /tmp
wget https://github.com/glpi-project/glpi/releases/download/10.0.18/glpi-10.0.18.tgz
wget https://github.com/glpi-project/glpi/releases/download/10.0.18/glpi-10.0.18.tgz.ascExtract the archive to the Apache web root:
sudo tar -xzf glpi-10.0.18.tgz -C /var/www/html/Set ownership and permissions so Apache can read and write the necessary directories:
sudo chown -R apache:apache /var/www/html/glpi
sudo find /var/www/html/glpi -type f -exec chmod 644 {} \;
sudo find /var/www/html/glpi -type d -exec chmod 755 {} \;Restore SELinux file context labels after placing files manually. Skipping this step is the most common reason GLPI returns a blank page or 403 error on SELinux-enforcing systems:
sudo restorecon -R /var/www/html/glpiStep 7: Configure the Apache Virtual Host for GLPI
A dedicated Apache virtual host keeps GLPI isolated from other web applications on the same server and makes DNS-based access straightforward.
Create the virtual host configuration file:
sudo nano /etc/httpd/conf.d/glpi.confAdd this block:
<VirtualHost *:80>
DocumentRoot /var/www/html/glpi
ServerName glpi.yourdomain.com
<Directory /var/www/html/glpi>
Options FollowSymLinks
AllowOverride All
Require all granted
</Directory>
ErrorLog /var/log/httpd/glpi-error.log
CustomLog /var/log/httpd/glpi-access.log combined
</VirtualHost>Replace glpi.yourdomain.com with your actual domain name or server IP address. The AllowOverride All directive enables .htaccess processing, which GLPI requires for its URL rewriting rules.
Test the Apache configuration for syntax errors before reloading:
sudo httpd -tA clean output shows Syntax OK. Now reload Apache:
sudo systemctl restart httpdStep 8: Run the GLPI Web Installation Wizard
Open a browser and navigate to your server:
http://your-server-ip/glpi/The GLPI installation wizard loads automatically. Work through each screen:
Wizard Steps
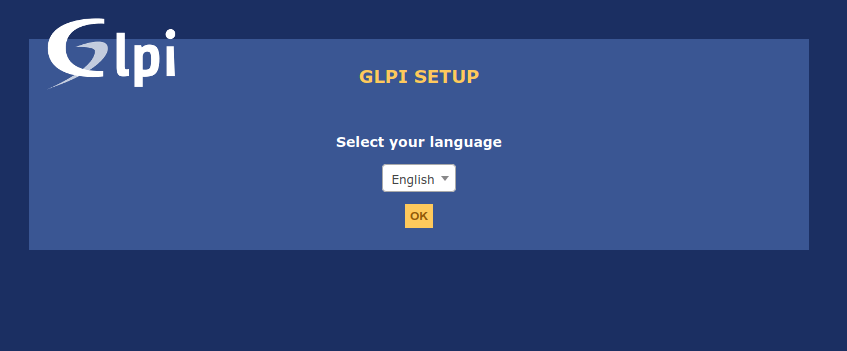
1. Language Selection
Choose your preferred language. This affects both the admin interface and default user-facing text throughout GLPI.
2. License Agreement
Accept the GNU GPL v2 license to continue.
3. System Requirements Check
The wizard scans your PHP modules, file permissions, and extensions. Every item should show green. If any item shows red, fix it before clicking Next. The most common issue at this stage is a missing PHP extension or incorrect file permissions.
4. Database Configuration
Enter the connection details you created in Step 3:
- SQL Server:
localhost - Database:
glpidb - Login:
glpiuser - Password:
YourSecurePassword123!
5. Database Initialization
GLPI creates all required tables and populates seed data. This takes anywhere from a few seconds to a couple of minutes depending on your hardware. Do not refresh the browser during this step.
6. Installation Complete
The wizard confirms success and displays default credentials.
Default Login Credentials
Change all of these immediately after your first login:
| Account | Username | Password | Role |
|---|---|---|---|
| Administrator | glpi |
glpi |
Full access |
| Technician | tech |
tech |
Helpdesk access |
| Normal User | normal |
normal |
Standard access |
| Read-Only | post-only |
postonly |
Ticket submission only |
Step 9: Post-Installation Security Hardening
A freshly installed GLPI is not production-ready until you complete these steps. Each one closes a real attack surface.
Remove the Install Directory
This is mandatory. Leaving the install directory accessible allows anyone to re-run the setup wizard and overwrite your database configuration.
sudo rm -rf /var/www/html/glpi/install/Change All Default Passwords
Log into the GLPI interface and navigate to Administration > Users. Change the password for every default account before you invite any team members in.
Enable HTTPS with Let’s Encrypt
Install Certbot and obtain a free SSL certificate:
sudo dnf install certbot python3-certbot-apache -y
sudo certbot --apache -d glpi.yourdomain.comCertbot automatically modifies your Apache virtual host to redirect HTTP to HTTPS and installs the certificate. It also schedules automatic renewal.
Review File Permissions
Make sure no files in the GLPI directory are world-writable:
sudo find /var/www/html/glpi -perm -o+w -type fAny output from this command identifies files that need tighter permissions.
Step 10: Configure Automated Backups
Backups protect your GLPI data from hardware failure, accidental deletion, and ransomware. Set up a simple daily backup script that covers both the database and uploaded files.
Create the backup script:
sudo nano /usr/local/bin/glpi-backup.shAdd this content:
#!/bin/bash
BACKUP_DIR="/var/backups/glpi"
DATE=$(date +%Y%m%d_%H%M%S)
mkdir -p $BACKUP_DIR
mysqldump -u glpiuser -p'YourSecurePassword123!' glpidb > $BACKUP_DIR/glpi_db_$DATE.sql
tar -czf $BACKUP_DIR/glpi_files_$DATE.tar.gz /var/www/html/glpi/files/
find $BACKUP_DIR -type f -mtime +7 -deleteMake it executable and schedule it:
sudo chmod +x /usr/local/bin/glpi-backup.sh
sudo crontab -eAdd this line to run the backup every night at 2:00 AM:
0 2 * * * /usr/local/bin/glpi-backup.shThe find ... -mtime +7 -delete line automatically removes backups older than seven days to prevent disk space from filling up over time.
Troubleshooting Common Issues
Database Connection Errors
If the wizard fails to connect to the database, start here:
sudo systemctl status mariadb
sudo tail -f /var/log/mariadb/mariadb.logDouble-check that the glpiuser account exists and has the correct privileges:
sudo mysql -u root -p -e "SHOW GRANTS FOR 'glpiuser'@'localhost';"403 Forbidden or Blank Page
This almost always points to SELinux blocking Apache. Check the audit log:
sudo audit2allow -a
sudo restorecon -R /var/www/html/glpiAlso confirm AllowOverride All is set in your virtual host and that .htaccess files are present in the GLPI root.
PHP Memory or Timeout Errors During Setup
Temporarily raise the limits in /etc/php.ini and retry:
max_execution_time = 10000
memory_limit = 512MRestart Apache after making changes:
sudo systemctl restart httpdFirewall Blocking Access
If the GLPI page does not load from a remote machine, verify the firewall rules applied:
sudo firewall-cmd --list-allHTTP and HTTPS should appear in the services line of the output.
Plugin Installation Failures
Always verify plugin compatibility with your installed GLPI version before installing. Check GLPI’s own PHP error log for specific error messages:
sudo tail -f /var/www/html/glpi/files/_log/php-errors.logPlugin errors are almost always version mismatches or missing PHP extensions.
Congratulations! You have successfully installed GLPI. Thanks for using this tutorial for installing GLPI on Fedora 43 Linux system. For additional help or useful information, we recommend you check the official GLPI website.