
Managing logs effectively is crucial for maintaining secure, reliable IT infrastructure. Graylog stands out as one of the most powerful open-source log management platforms available today, offering real-time log collection, indexing, analysis, and alerting capabilities. Whether you’re a system administrator, DevOps engineer, or security professional, Graylog provides the tools needed to monitor applications, troubleshoot issues, and detect security threats across your entire infrastructure.
This comprehensive guide walks you through installing Graylog on Fedora 43, covering everything from initial system preparation to accessing your fully functional log management dashboard. You’ll learn how to configure the required components—Java, MongoDB, OpenSearch, and the Graylog server itself—with detailed commands and explanations at every step. By the end of this tutorial, you’ll have a production-ready Graylog installation capable of collecting and analyzing logs from multiple sources across your network.
Prerequisites
Before beginning the Graylog installation process, ensure your system meets the necessary requirements for optimal performance and stability.
System Requirements
Your Fedora 43 server should have at minimum a dual-core processor and 4 GB of RAM, though 8 GB is strongly recommended for production environments. Allocate at least 20 GB of disk space for the operating system, applications, and initial log storage. Keep in mind that log data can grow rapidly depending on your environment, so plan storage capacity accordingly.
You’ll need root or sudo privileges to install packages and modify system configurations. A stable internet connection is essential for downloading software packages and repository metadata. Verify your Fedora 43 installation is up to date before proceeding with the Graylog setup.
Required Network Ports
Graylog and its dependencies communicate over several network ports that must be accessible. Port 9000 serves the Graylog web interface where you’ll access dashboards and configure the system. OpenSearch operates on port 9200 for indexing and searching log data. MongoDB uses port 27017 for storing Graylog’s configuration and metadata. Understanding these port requirements helps you configure firewalls and security groups appropriately.
Preparing Your Fedora 43 Server
Proper system preparation ensures a smooth installation process and reduces potential conflicts.
System Update
Start by updating all existing packages to their latest versions. Open your terminal and run:
sudo dnf update -yThis command refreshes repository metadata and upgrades installed packages. The -y flag automatically confirms the updates without prompting. After the update completes, reboot your server if kernel updates were applied to ensure you’re running the latest system components.
Creating a Dedicated User
Following security best practices, create a dedicated user account for managing Graylog operations:
sudo useradd -m -s /bin/bash graylogadmin
sudo passwd graylogadmin
sudo usermod -aG wheel graylogadminThese commands create a new user with a home directory, set a password, and grant sudo privileges by adding the user to the wheel group. Using a dedicated account instead of root minimizes security risks.
Firewall Configuration
Configure the Fedora firewall to allow traffic to Graylog services:
sudo firewall-cmd --permanent --add-port=9000/tcp
sudo firewall-cmd --permanent --add-port=9200/tcp
sudo firewall-cmd --permanent --add-port=27017/tcp
sudo firewall-cmd --reloadThe --permanent flag ensures these rules persist across reboots. Verify your configuration with sudo firewall-cmd --list-ports to confirm all required ports are open.
Step 1: Installing Java
Graylog requires Java to run, specifically OpenJDK version 17 or later. Check if Java is already installed:
java -versionIf Java isn’t present or you have an older version, install OpenJDK 17:
sudo dnf install java-17-openjdk java-17-openjdk-devel -yThis installs both the Java runtime environment and development tools. Verify the installation succeeded:
java -versionSet the JAVA_HOME environment variable by adding it to your shell profile:
echo 'export JAVA_HOME=/usr/lib/jvm/java-17-openjdk' >> ~/.bashrc
source ~/.bashrcThis ensures Java is properly configured for Graylog and other applications.
Step 2: Installing and Configuring MongoDB
MongoDB serves as Graylog’s configuration and metadata storage backend, maintaining information about users, streams, dashboards, and system settings.
Adding MongoDB Repository
Fedora repositories might not include the latest MongoDB versions. Add the official MongoDB repository:
sudo tee /etc/yum.repos.d/mongodb-org-6.0.repo << EOF
[mongodb-org-6.0]
name=MongoDB Repository
baseurl=https://repo.mongodb.org/yum/redhat/8/mongodb-org/6.0/x86_64/
gpgcheck=1
enabled=1
gpgkey=https://www.mongodb.org/static/pgp/server-6.0.asc
EOFThis configuration creates a repository file pointing to MongoDB 6.0 packages. The GPG key ensures package authenticity.
Installing MongoDB
Install MongoDB with all necessary components:
sudo dnf install mongodb-org -yThe installation includes the MongoDB server, client tools, and dependencies. This process typically takes a few minutes depending on your connection speed.
Starting and Enabling MongoDB
Launch MongoDB and configure it to start automatically on boot:
sudo systemctl start mongod
sudo systemctl enable mongodCheck the service status to confirm MongoDB is running:
sudo systemctl status mongodYou should see an “active (running)” status. If the service fails to start, check /var/log/mongodb/mongod.log for error messages.
Step 3: Installing and Configuring OpenSearch
OpenSearch is the search and analytics engine that stores and indexes all log data collected by Graylog. It’s a community-driven fork of Elasticsearch, offering full compatibility with Graylog.
Understanding OpenSearch vs Elasticsearch
While Graylog supports both OpenSearch and Elasticsearch, OpenSearch is recommended for new installations due to licensing considerations and strong community support. OpenSearch provides the same powerful indexing and search capabilities Graylog needs to handle large volumes of log data efficiently.
Downloading OpenSearch
Download the OpenSearch RPM package directly from the official repository:
wget https://artifacts.opensearch.org/releases/bundle/opensearch/2.11.1/opensearch-2.11.1-linux-x64.rpmInstall the package using the rpm command:
sudo rpm -ivh opensearch-2.11.1-linux-x64.rpmThis installs OpenSearch to /usr/share/opensearch with configuration files in /etc/opensearch.
Configuring OpenSearch
Edit the main OpenSearch configuration file:
sudo nano /etc/opensearch/opensearch.ymlModify or add these essential settings:
cluster.name: graylog-cluster
node.name: node-1
network.host: 127.0.0.1
discovery.type: single-node
action.auto_create_index: falseThe cluster name groups OpenSearch nodes together, while the node name identifies this specific instance. Setting network.host to 127.0.0.1 restricts access to localhost for security. The action.auto_create_index: false setting prevents automatic index creation, which is important for Graylog’s index management strategy.
JVM Heap Size Optimization
OpenSearch performance depends heavily on proper JVM heap configuration. Edit the JVM options:
sudo nano /etc/opensearch/jvm.optionsSet heap size to approximately half of your available RAM, with a maximum of 32 GB:
-Xms2g
-Xmx2gThese values allocate 2 GB of heap space. On systems with 8 GB RAM, you might increase this to 4 GB. Keep minimum and maximum heap sizes identical to prevent JVM resizing overhead.
Starting OpenSearch Service
Enable and start OpenSearch:
sudo systemctl daemon-reload
sudo systemctl start opensearch
sudo systemctl enable opensearchVerify OpenSearch is running and responding:
curl -X GET http://127.0.0.1:9200You should receive JSON output showing cluster information. If the connection fails, check OpenSearch logs at /var/log/opensearch/graylog-cluster.log.
Step 4: Adding Graylog Repository
Graylog provides official package repositories for easier installation and updates.
Importing GPG Key
Import the Graylog repository GPG key to verify package signatures:
sudo rpm --import https://packages.graylog2.org/repo/el/8/RPM-GPG-KEY-graylogThis security measure ensures you’re installing authentic Graylog packages.
Creating Repository File
Create the Graylog repository configuration:
sudo tee /etc/yum.repos.d/graylog.repo << EOF
[graylog]
name=graylog
baseurl=https://packages.graylog2.org/repo/el/stable/5.2/\$basearch/
gpgcheck=1
gpgkey=file:///etc/pki/rpm-gpg/RPM-GPG-KEY-graylog
enabled=1
EOFThis repository provides access to Graylog 5.2 packages. The configuration works with Fedora 43 despite referencing the EL (Enterprise Linux) repository path.
Updating Package Cache
Refresh DNF metadata to include the new repository:
sudo dnf makecacheThis command downloads repository metadata without installing packages, ensuring Graylog packages are available for installation.
Step 5: Installing Graylog Server
With all dependencies in place, install the Graylog server package:
sudo dnf install graylog-server -yThe installation places Graylog binaries in /usr/share/graylog-server, configuration files in /etc/graylog/server, and creates necessary system users. Graylog Open is the community edition offering all core features. Enterprise editions provide additional features like advanced reporting and archiving capabilities.
Step 6: Configuring Graylog Server
Proper configuration is critical for Graylog to communicate with MongoDB and OpenSearch while providing secure web access.
Editing Main Configuration File
Open the Graylog server configuration:
sudo nano /etc/graylog/server/server.confThis file contains dozens of parameters controlling Graylog’s behavior. We’ll focus on the essential settings required to get Graylog running.
Setting HTTP Bind Address
Locate and modify the HTTP bind address setting:
http_bind_address = 0.0.0.0:9000Using 0.0.0.0 allows connections from any network interface. For security in production environments, replace this with your server’s specific IP address. Port 9000 is the standard Graylog web interface port.
Generating Password Secret
Generate a secure password secret for encrypting user passwords:
pwgen -N 1 -s 96If pwgen isn’t installed, use OpenSSL instead:
openssl rand -base64 96 | tr -d '\n'Copy the output and add it to server.conf:
password_secret = your_generated_secret_hereThis secret must remain confidential and consistent. Changing it invalidates existing user passwords.
Creating Admin Password Hash
Generate a SHA256 hash for the admin password. Choose a strong password and hash it:
echo -n "YourStrongPassword" | sha256sum | cut -d" " -f1Add the resulting hash to server.conf:
root_password_sha2 = your_password_hash_hereThe admin username is “admin” by default. You’ll use these credentials for initial login.
Configuring OpenSearch Connection
Tell Graylog where to find OpenSearch:
elasticsearch_hosts = http://127.0.0.1:9200Despite the parameter name referencing Elasticsearch, it works with OpenSearch. For multiple OpenSearch nodes, provide a comma-separated list of URLs.
Optional Email Configuration
For email alerts and notifications, configure SMTP settings:
transport_email_enabled = true
transport_email_hostname = smtp.example.com
transport_email_port = 587
transport_email_use_auth = true
transport_email_auth_username = your_email@example.com
transport_email_auth_password = your_email_password
transport_email_from_email = graylog@example.comEmail configuration can be completed later if you’re not ready to set it up immediately.
Step 7: Starting Graylog Services
Launch Graylog and configure it for automatic startup.
Enabling and Starting Graylog
Reload systemd to recognize Graylog’s service file:
sudo systemctl daemon-reloadStart the Graylog server:
sudo systemctl start graylog-serverEnable automatic startup on boot:
sudo systemctl enable graylog-serverThese commands initialize Graylog’s startup sequence.
Verifying Service Status
Check that Graylog started successfully:
sudo systemctl status graylog-serverLook for “active (running)” status. Graylog’s initialization can take several minutes as it creates initial indexes in OpenSearch and performs first-time setup tasks. Monitor the startup process:
sudo tail -f /var/log/graylog-server/server.logWatch for messages indicating successful startup. The log shows connections to MongoDB and OpenSearch, index creation, and web interface availability.
Step 8: Accessing Graylog Web Interface
With all services running, access your Graylog installation through a web browser.
Initial Login
Navigate to your server’s IP address on port 9000:
http://your_server_ip:9000The Graylog login page appears. Enter “admin” as the username and the password you hashed in the configuration step. Remember to use the actual password, not the hash.
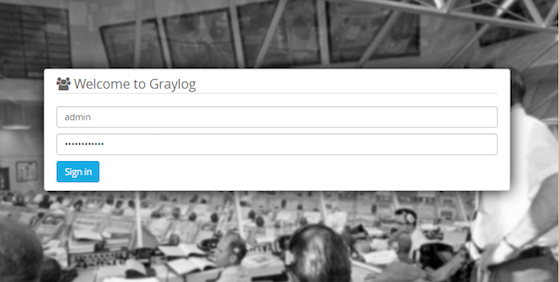
Web Interface Overview
After logging in, you’ll see the Graylog dashboard with several main sections. The Search page allows querying collected logs with powerful filtering capabilities. Streams organize logs into categories based on rules you define. Alerts notify you when specific conditions are met in your log data. The System section provides server health information and configuration options.
Creating Additional Users
Navigate to System → Users to create additional user accounts. Assign appropriate roles to limit access based on user responsibilities. Avoid sharing the admin account for day-to-day operations. Role-based access control helps maintain security while giving team members the access they need.
Post-Installation Configuration
A fresh Graylog installation needs additional configuration to begin collecting logs.
Setting Up Inputs
Inputs define how Graylog receives log data. Navigate to System → Inputs to create your first input. Common input types include Syslog UDP/TCP for traditional syslog messages, GELF for structured logging, and Beats for Elastic Beats agents. Click “Select input” and choose an input type appropriate for your environment.
Configure the input settings including the port number and bind address. Start the input to begin accepting log messages. Each input can buffer messages, parse specific formats, and extract fields automatically.
Creating Data Streams
Streams route incoming messages to specific destinations based on rules. Navigate to Streams and create a new stream. Define rules matching specific log characteristics like source IP addresses, log levels, or message content patterns. Streams help organize logs from different applications or servers, making searches more efficient.
Configuring Retention Policies
Index sets control how long Graylog retains log data. Navigate to System → Indices to view and modify the default index set. Configure rotation strategies determining when to create new indexes based on size or time. Set retention policies to delete old indexes automatically, preventing unlimited storage growth. Balance retention duration with available disk space and compliance requirements.
Security Hardening
Strengthen your Graylog installation’s security posture with these additional measures.
SSL/TLS Configuration
Protect sensitive log data and credentials by enabling HTTPS. Generate or obtain an SSL certificate for your Graylog server. Modify server.conf to enable HTTP TLS and specify certificate paths. Update the http_bind_address to use HTTPS URLs. Restart Graylog to apply SSL settings.
Firewall Best Practices
Restrict port 9000 access to specific IP addresses or networks using firewall rules. Only allow trusted administrators to access the web interface. Keep OpenSearch and MongoDB ports closed to external networks since Graylog communicates with them locally. Configure SELinux policies if using enforcing mode on Fedora to permit necessary Graylog operations.
Regular Updates
Keep Graylog and its dependencies current with security patches. Subscribe to Graylog’s security mailing list for vulnerability announcements. Test updates in non-production environments before applying them to critical systems. Regular maintenance prevents security incidents and ensures optimal performance.
Troubleshooting Common Issues
Resolve common problems that may occur during or after installation.
Service Won’t Start
If Graylog fails to start, verify MongoDB and OpenSearch are running first. Check service status for each component. Review Graylog logs at /var/log/graylog-server/server.log for specific error messages. Insufficient memory can prevent services from starting—verify your system meets minimum requirements.
Cannot Access Web Interface
When the web interface is unreachable, confirm the firewall allows port 9000 traffic. Verify http_bind_address in server.conf matches your server’s network configuration. Test network connectivity from your workstation to the server. Some browsers cache aggressively—try accessing Graylog from an incognito window or different browser.
OpenSearch Connection Failures
Connection errors between Graylog and OpenSearch often stem from misconfigured elasticsearch_hosts settings. Verify OpenSearch is listening on the configured address and port. Check OpenSearch logs for startup errors or cluster health issues. Network firewalls or SELinux policies might block local connections.
Performance Problems
Slow searches or high resource usage indicate optimization opportunities. Review JVM heap sizes for both OpenSearch and Graylog. Monitor system resources using htop or similar tools to identify bottlenecks. Optimize index settings and reduce retention periods if disk I/O is saturated. Consider scaling to multiple OpenSearch nodes for larger deployments.
Congratulations! You have successfully installed Graylog. Thanks for using this tutorial for installing Graylog free and open log management on Fedora 43 Linux system. For additional help or useful information, we recommend you check the official Graylog website.

