How To Install OpenSCAP on Ubuntu 22.04 LTS

In this tutorial, we will show you how to install OpenSCAP on Ubuntu 22.04 LTS. OpenSCAP provides a powerful toolset for performing security audits and vulnerability assessments on Linux systems. This comprehensive guide will walk you through the process of installing and configuring OpenSCAP on Ubuntu 22.04 LTS (Jammy Jellyfish), enabling you to enforce security compliance and identify potential vulnerabilities in your system.
Understanding OpenSCAP
OpenSCAP is an open-source security auditing and vulnerability scanning tool based on the Security Content Automation Protocol (SCAP). It integrates with various security specifications including OVAL (Open Vulnerability and Assessment Language), XCCDF (Extensible Configuration Checklist Description Format), CPE (Common Platform Enumeration), CCE (Common Configuration Enumeration), and CVSS (Common Vulnerability Scoring System). These components work together to create comprehensive security checklists that can be processed by SCAP-validated products.
The tool serves as both a library and a command-line utility that helps system administrators check their systems against established security benchmarks. Its primary function is to evaluate security compliance and identify vulnerabilities that could potentially compromise your system’s integrity.
Prerequisites
Before proceeding with the installation, ensure your system meets the following requirements:
- A server running Ubuntu 22.04 LTS (Jammy Jellyfish)
- Root access or a user with sudo privileges
- Active internet connection for downloading packages
- At least 66MB of available disk space for installation
It’s generally recommended to use a fresh installation of Ubuntu 22.04 to prevent potential conflicts with existing configurations. If you’re working with a production system, consider testing the installation process in a controlled environment first.
System Preparation
The first step involves updating your system and installing necessary dependencies. Open a terminal and run the following commands:
sudo apt update
sudo apt upgrade
sudo apt install wget apt-transport-https gnupg2 software-properties-commonThese commands update your package lists, upgrade existing packages, and install essential utilities needed for the OpenSCAP installation process. The system update ensures compatibility with the latest packages and fixes any security vulnerabilities in your current system.
Creating a backup of critical system configurations is also advisable before proceeding with security hardening tools. This provides a restoration point if anything goes wrong during the installation or subsequent scanning processes.
Installing Core OpenSCAP Components
OpenSCAP is available in the default Ubuntu 22.04 repositories, making the installation straightforward. Install the core components with the following command:
sudo apt install libopenscap8 bzip2This command installs the libopenscap8 package, which contains the OpenSCAP library and command-line tool. The bzip2 utility is included to handle compressed files you might encounter when working with security content.
After installation, verify that OpenSCAP has been installed correctly by checking its version:
oscap --versionThe output will display the supported specifications, capabilities, paths to important files, inbuilt CPE names, and supported OVAL objects. This information is useful for understanding the tool’s capabilities and configuration.
Working with Security Profiles
One challenge with Ubuntu 22.04 is the limited availability of the SCAP Security Guide (SSG) packages in the default repositories. When attempting to install scap-security-guide on Ubuntu 22.04, you may encounter errors indicating that the package cannot be found.
There are several alternatives for obtaining security profiles:
- Compile from source: Since the project is open-source, you can download and compile the profiles from the ComplianceAsCode/content repository.
- Use precompiled assets: Security profiles are available as precompiled assets from the git repository, which can be downloaded and used with OpenSCAP.
- Ubuntu Security Guide with Ubuntu Pro: If you have Ubuntu Pro, you can enable and install the Ubuntu Security Guide (USG).
For organizations requiring strict compliance checking, building from source might be the most reliable approach, though it requires more technical expertise.
Performing Your First Security Scan
To perform a basic security scan, you’ll need to download OVAL content from Canonical. Run the following command:
wget https://people.canonical.com/~ubuntu-security/oval/com.ubuntu.xenial.cve.oval.xmlThis downloads the OVAL definitions file, which contains vulnerability information specific to Ubuntu systems. While this example uses Xenial content, you should check for more current content for Jammy Jellyfish if available.
Now, run a system audit using the downloaded OVAL content:
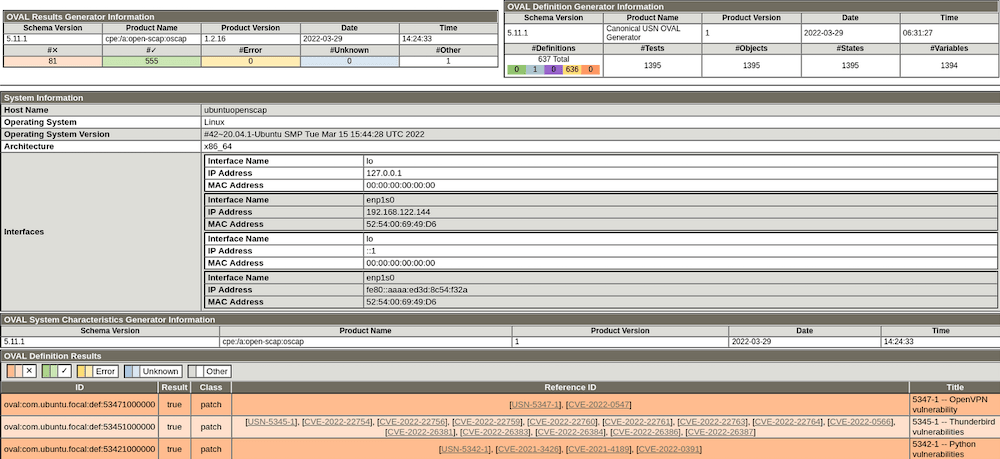
oscap oval eval --results /tmp/oscap_results.xml --report /tmp/oscap_report.html com.ubuntu.xenial.cve.oval.xmlThis command evaluates your system against the OVAL definitions and generates both XML results and an HTML report. The XML file contains detailed technical information, while the HTML report provides a more user-friendly visualization of the results.
To view the HTML report, you can copy it to a web-accessible location or open it directly in a browser:
sudo cp /tmp/oscap_report.html /var/www/htmlNavigate to http://your-server-ip/oscap_report.html in your web browser to view the report.
Advanced Configuration and Usage
Once you’re familiar with basic scanning, you can explore more advanced OpenSCAP features:
Working with Different Security Benchmarks
Different organizations follow various security standards like CIS Benchmarks, DISA STIGs, or PCI-DSS. OpenSCAP supports evaluating your system against these standards when the appropriate profiles are available.
For example, to run a scan using a specific profile:
sudo oscap xccdf eval --profile xccdf_org.ssgproject.content_profile_standard --results results.xml --report report.html path/to/content.xmlAutomating Security Scans
Regular security auditing is essential for maintaining system security. You can automate OpenSCAP scans using cron jobs:
0 2 * * 0 /usr/bin/oscap oval eval --results /var/log/scap/results-$(date +\%Y\%m\%d).xml --report /var/log/scap/report-$(date +\%Y\%m\%d).html /path/to/oval-content.xmlThis cron entry schedules a weekly scan at 2 AM every Sunday and stores the results with datestamped filenames.
Troubleshooting Common Issues
When working with OpenSCAP on Ubuntu 22.04, you might encounter these common issues:
Package Availability Problems
As mentioned earlier, the scap-security-guide package might not be available in standard repositories. Alternative approaches include compiling from source or using precompiled assets.
“Not Applicable” Results
Many scan results might show as “not applicable.” This is normal and indicates that certain checks are not relevant to your system configuration or installed packages.
Profile Compatibility Issues
Some profiles might not be fully compatible with Ubuntu 22.04. In such cases, you may need to modify profiles or use Ubuntu-specific profiles when available.
Scan Performance Concerns
Security scans can be resource-intensive. If performance is an issue, consider scheduling scans during off-peak hours or limiting the scope of scans to focus on critical systems only.
Congratulations! You have successfully installed OpenSCAP. Thanks for using this tutorial for installing OpenSCAP security audits on Ubuntu 22.04 LTS Jammy Jellyfish system. For additional help or useful information, we recommend you check the official OpenSCAP website.