
In this tutorial, we will show you how to install Passbolt on AlmaLinux 8. For those of you who didn’t know, Passbolt is a free and open-source password manager based on PHP, MySQL, and OpenPGP which allows you to securely store and share login credentials of website, router password, Wi-Fi password, etc. It is self-hosted and available in both community and subscription-based editions.
This article assumes you have at least basic knowledge of Linux, know how to use the shell, and most importantly, you host your site on your own VPS. The installation is quite simple and assumes you are running in the root account, if not you may need to add ‘sudo‘ to the commands to get root privileges. I will show you through the step-by-step installation of the Passbolt password manager on an AlmaLinux 8. You can follow the same instructions for Fedora, RHEL, CentOS, and Rocky Linux distributions.
Prerequisites
- A server running one of the following operating systems: AlmaLinux 8, CentOS, and Rocky Linux 8.
- It’s recommended that you use a fresh OS install to prevent any potential issues
- A
non-root sudo useror access to theroot user. We recommend acting as anon-root sudo user, however, as you can harm your system if you’re not careful when acting as the root.
Install Passbolt on AlmaLinux 8
Step 1. First, let’s start by ensuring your system is up-to-date.
sudo dnf clean all sudo dnf update
Step 2. Installing a LEMP server.
Before installing Passbolt, a Fedora LEMP server is be required. If you do not have LAMP installed, you can follow our guide here.
Step 3. Installing PHP composer.
Run the following command to download the PHP composer installer script:
php -r "copy('https://getcomposer.org/installer', 'composer-setup.php');"
php -r "if (hash_file('sha384', 'composer-setup.php') === '906a84df04cea2aa72f40b5f787e49f22d4c2f19492ac310e8cba5b96ac8b64115ac402c8cd292b8a03482574915d1a8') { echo 'Installer verified'; } else { echo 'Installer corrupt'; unlink('composer-setup.php'); } echo PHP_EOL;"
After that, execute again the following command to install the PHP composer:
php composer-setup.php sudo mv composer.phar /usr/bin/composer
Verify PHP composer:
sudo -u nginx composer --version
Next, install the GnuPG PHP Extensions from the PHP Extension Community Library (PECL) repository:
pecl install gnupg echo "extension=gnupg.so" > /etc/php.d/gnupg.ini
Step 4. Installing Passbolt on AlmaLinux 8.
By default, Passbolt is not available on the AlmaLinux 8 base repository. Now we run the following command to clone the latest version of Passbolt from the GitHub page:
cd /var/www/ git clone https://github.com/passbolt/passbolt_api.git passbolt
We will need to change some folders permissions:
sudo chown -R nginx:nginx /var/www/passbolt
Next, move to the Passbolt installation directory and install PHP dependencies using the PHP composer command:
cd /var/www/passbolt sudo -u nginx composer install --no-dev
Step 5. Generate GPG Key for Server.
Now we generate a new GPG key for the Passbolt server:
gpg --gen-key
Output:
gpg (GnuPG) 2.2.20; Copyright (C) 2020 Free Software Foundation, Inc. This is free software: you are free to change and redistribute it. There is NO WARRANTY, to the extent permitted by law. Note: Use "gpg --full-generate-key" for a full featured key generation dialog. GnuPG needs to construct a user ID to identify your key. Real name: godet Email address: godet@idroot.us You selected this USER-ID: "godet <godet@idroot.us>" Change (N)ame, (E)mail, or (O)kay/(Q)uit? O We need to generate a lot of random bytes. It is a good idea to perform some other action (type on the keyboard, move the mouse, utilize the disks) during the prime generation; this gives the random number generator a better chance to gain enough entropy. We need to generate a lot of random bytes. It is a good idea to perform some other action (type on the keyboard, move the mouse, utilize the disks) during the prime generation; this gives the random number generator a better chance to gain enough entropy. gpg: key 14F31ED1FBEBAD9A marked as ultimately trusted gpg: revocation certificate stored as '/root/.gnupg/openpgp-revocs.d/BCD52DF829FF8F9408A2F1B214F31ED1FBEBAD9A.rev' public and secret key created and signed. pub rsa2048 2022-03-26 [SC] [expires: 2024-03-26] GDT52DF829FF8F9408A2F1B214F31ED1FBEBABTC uid godet <godet@idroot.us> sub rsa2048 2022-03-26 [E] [expires: 2024-03-26]
After that, export the GPG key to the Passbolt installation directory ‘/var/www/passbolt/config/gpg/‘:
gpg --armor --export-secret-keys godet@idroot.us > /var/www/passbolt/config/gpg/serverkey_private.asc gpg --armor --export godet@idroot.us > /var/www/passbolt/config/gpg/serverkey.asc
*Note about your GPG key information:
- Fingerprint: GDT52DF829FF8F9408A2F1B214F31ED1FBEBABTC
- Email: godet@idroot.us
- Public key: serverkey.asc
- Private key: serverkey_private.asc
Next, generate the GNUPG directory for the user Nginx using the following command:
sudo su -s /bin/bash -c "gpg --list-keys" nginx
Step 6. Configuring MariaDB.
By default, MariaDB is not hardened. You can secure MariaDB using the mysql_secure_installation script. you should read and below each step carefully which will set a root password, remove anonymous users, disallow remote root login, and remove the test database and access to secure MariaDB:
mysql_secure_installation
Configure it like this:
- Set root password? [Y/n] y - Remove anonymous users? [Y/n] y - Disallow root login remotely? [Y/n] y - Remove test database and access to it? [Y/n] y - Reload privilege tables now? [Y/n] y
Next, we will need to log in to the MariaDB console and create a database for Passbolt. Run the following command:
mysql -u root -p
This will prompt you for a password, so enter your MariaDB root password and hit Enter. Once you are logged in to your database server you need to create a database for Passbolt installation:
MariaDB [(none)]> CREATE DATABASE passbolt_db; MariaDB [(none)]> CREATE USER 'passbolt'@'localhost' IDENTIFIED BY 'your-strong-password'; MariaDB [(none)]> GRANT ALL PRIVILEGES ON passbolt_db.* TO 'passbolt'@'localhost' IDENTIFIED BY 'your-strong-password' WITH GRANT OPTION; MariaDB [(none)]> ALTER DATABASE passbolt_db charset=utf8; MariaDB [(none)]> FLUSH PRIVILEGES; MariaDB [(none)]> EXIT;
Step 7. Configure Nginx for Passbolt.
Now we create an Nginx configuration file for Passbolt:
export PASSBOLT=/var/www/passbolt/ cd $PASSBOLT cp config/passbolt.default.php config/passbolt.php nano config/passbolt.php
Change the ‘fullBaseUrl‘ option with your Passbolt domain name:
'App' => [ // comment 'fullBaseUrl' => 'https://pass.your-domain.com', // comment.. ],
Next, change the database configuration:
// Database configuration. 'Datasources' => [ 'default' => [ 'host' => 'localhost', //'port' => 'non_standard_port_number', 'username' => 'passbolt', 'password' => 'your-strong-password', 'database' => 'passbolt_db', ], ],
After that, copy and paste your GPG fingerprint and uncomment the ‘public’ and ‘private’ options:
gpg' => [ // // COMMENT REMOVED // 'serverKey' => [ // Server private key fingerprint. 'fingerprint' => '38E3736DD02860F8CBA57BB99C8B82A2C3A69BMW', 'public' => CONFIG . 'gpg' . DS . 'serverkey.asc', 'private' => CONFIG . 'gpg' . DS . 'serverkey_private.asc', ],
Save and close the file, then create a new Nginx server blocks configuration:
nano /etc/nginx/conf.d/passbolt.conf
Add the following file:
server {
listen 80;
server_name pass.your-domain.com;
return 302 https://$server_name$request_uri;
}
server {
listen 443 ssl http2;
server_name pass.your-domain.com;
root /var/www/passbolt;
ssl_certificate /etc/letsencrypt/live/pass.your-domain.com/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/live/pass.your-domain.com/privkey.pem;
ssl_protocols TLSv1.2;
ssl_prefer_server_ciphers on;
ssl_ciphers ECDHE-RSA-AES256-GCM-SHA512:DHE-RSA-AES256-GCM-SHA512:ECDHE-RSA-AES256-GCM-SHA384:DHE-RSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-SHA384;
ssl_ecdh_curve secp384r1; # Requires nginx >= 1.1.0
ssl_session_timeout 10m;
ssl_session_cache shared:SSL:10m;
ssl_session_tickets off; # Requires nginx >= 1.5.9
# ssl_stapling on; # Requires nginx >= 1.3.7
# ssl_stapling_verify on; # Requires nginx => 1.3.7
resolver 8.8.8.8 8.8.4.4 valid=300s;
resolver_timeout 5s;
add_header X-Frame-Options DENY;
add_header X-Content-Type-Options nosniff;
add_header X-XSS-Protection "1; mode=block";
location / {
try_files $uri $uri/ /index.php?$args;
index index.php;
}
location ~ \.php$ {
fastcgi_index index.php;
fastcgi_pass unix:/var/run/php-fpm/www.sock;
fastcgi_split_path_info ^(.+\.php)(.+)$;
include fastcgi_params;
fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name;
fastcgi_param SERVER_NAME $http_host;
}
location ~* \.(jpe?g|woff|woff2|ttf|gif|png|bmp|ico|css|js|json|pdf|zip|htm|html|docx?|xlsx?|pptx?|txt|wav|swf|svg|avi|mp\d)$ {
access_log off;
log_not_found off;
try_files $uri /webroot/$uri /index.php?$args;
}
}
Save and close the file, then restart the Nginx service for the changes to take effect:
nginx -t sudo systemctl restart nginx
Finally, start the Passbolt installation using the command as below:
cd /var/www/passbolt sudo su -s /bin/bash -c "./bin/cake passbolt install" nginx
You should get the following output:
--------------------------------------------------------------- User saved successfully. To start registration follow the link provided in your mailbox or here: https://pass.your-domain.com/setup/install/f82227bc-b0b6-bmw-99a7-6b490a4ba262/5a112de0-e46-4e1b-97c8-26453ef120
Step 8. Configure Firewall.
Allow the firewall to HTTP and HTTPS and reload it with the following commands:
sudo firewall-cmd --permanent --zone=public --add-service=http sudo firewall-cmd --permanent --zone=public --add-service=https sudo firewall-cmd --reload
Step 9. Accessing Passbolt Web Interface.
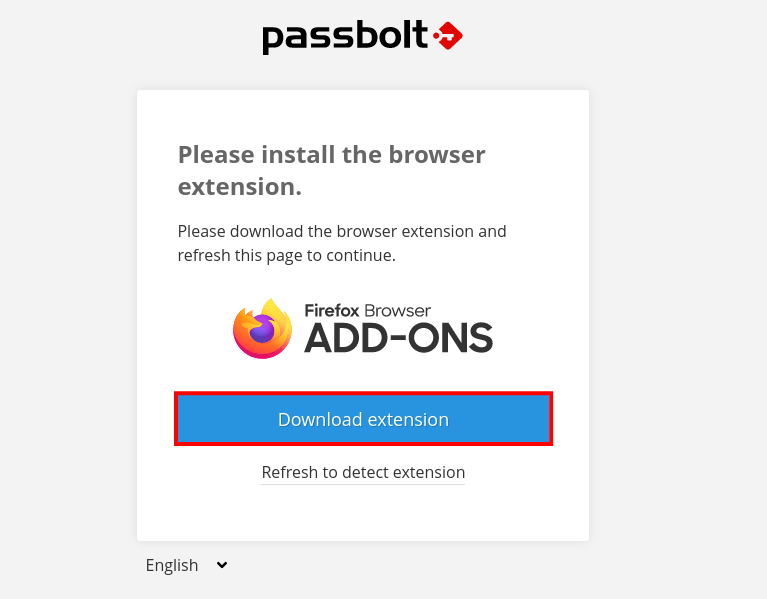
Once successfully installed, open your web browser and access the Passbolt using the URL https://pass.your-domain.com/setup/install/f82227bc-b0b6-bmw-99a7-6b490a4ba262/5a112de0-e46-4e1b-97c8-26453ef120. You will be redirected to the following page:
Congratulations! You have successfully installed Passbolt. Thanks for using this tutorial for installing the Passbolt password manager on your AlmaLinux 8 system. For additional help or useful information, we recommend you check the official Passbolt website.
[su_box title=”VPS Manage Service Offer” style=”bubbles” box_color=”#000000″ radius=”10″]If you don’t have time to do all of this stuff, or if this is not your area of expertise, we offer a service to do “VPS Manage Service Offer”, starting from $10 (Paypal payment). Please contact us to get the best deal![/su_box]

