
In this tutorial, we will show you how to install SpiderFoot on Ubuntu 20.04 LTS. For those of you who didn’t know, Spiderfoot is a free source testing tool to analyze any vulnerabilities/malicious functions on the server to reduce the attacks. It is written in Python and uses SQLite as a database backend. It provides a web-based interface to perform penetration testing for more than one target simultaneously through a web browser.
This article assumes you have at least basic knowledge of Linux, know how to use the shell, and most importantly, you host your site on your own VPS. The installation is quite simple and assumes you are running in the root account, if not you may need to add ‘sudo‘ to the commands to get root privileges. I will show you the step-by-step installation of the SpiderFoot on Ubuntu 20.04 (Focal Fossa). You can follow the same instructions for Ubuntu 18.04, 16.04, and any other Debian-based distribution like Linux Mint.
Prerequisites
- A server running one of the following operating systems: Ubuntu 20.04 LTS (Focal Fossa).
- It’s recommended that you use a fresh OS install to prevent any potential issues.
- SSH access to the server (or just open Terminal if you’re on a desktop).
- A
non-root sudo useror access to theroot user. We recommend acting as anon-root sudo user, however, as you can harm your system if you’re not careful when acting as the root.
Install SpiderFoot on Ubuntu 20.04 LTS Focal Fossa
Step 1. Update Your Ubuntu system.
First, make sure that all your system packages are up-to-date by running the following apt commands in the terminal.
sudo apt update sudo apt upgrade
Step 2. Installing Python.
SpiderFoot is written in Python and required to be installed on your system:
sudo apt install python3 python3-pip
Step 3. Installing SpiderFoot on Ubuntu 20.04.
Now we download the latest version of Spiderfoot from the Git repository:
wget https://github.com/smicallef/spiderfoot/archive/v3.3.tar.gz
Next, extract the downloaded archive:
tar -xvzf v3.3.tar.gz cd spiderfoot-3.3 pip3 install -r requirements.txt
Once installed, you can list all options available with SpiderFoot using the following command:
python3 sf.py --help
You should get the following output:
usage: sf.py [-h] [-d] [-l IP:port] [-m mod1,mod2,...] [-M] [-s TARGET] [-t type1,type2,...] [-T] [-o tab|csv|json] [-H] [-n] [-r]
[-S LENGTH] [-D DELIMITER] [-f] [-F type1,type2,...] [-x] [-q]
SpiderFoot 3.3: Open Source Intelligence Automation.
optional arguments:
-h, --help show this help message and exit
-d, --debug Enable debug output.
-l IP:port IP and port to listen on.
-m mod1,mod2,... Modules to enable.
-M, --modules List available modules.
-s TARGET Target for the scan.
-t type1,type2,... Event types to collect (modules selected automatically).
-T, --types List available event types.
-o tab|csv|json Output format. Tab is default. If using json, -q is enforced.
-H Don't print field headers, just data.
-n Strip newlines from data.
-r Include the source data field in tab/csv output.
-S LENGTH Maximum data length to display. By default, all data is shown.
-D DELIMITER Delimiter to use for CSV output. Default is ,.
-f Filter out other event types that weren't requested with -t.
-F type1,type2,... Show only a set of event types, comma-separated.
-x STRICT MODE. Will only enable modules that can directly consume your target, and if -t was specified only those events
will be consumed by modules. This overrides -t and -m options.
-q Disable logging. This will also hide errors!
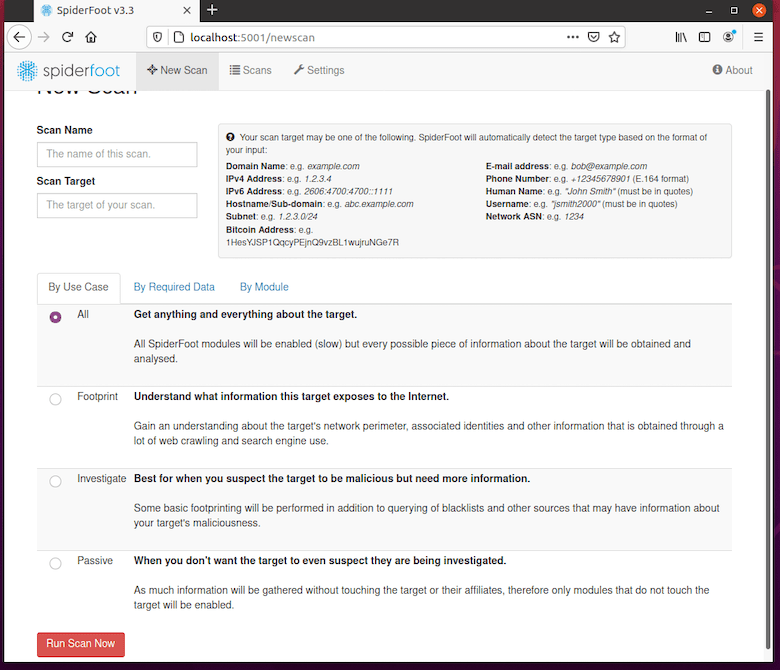
SpiderFoot also has a web interface. Run the commands initial the web UI:
python3 sf.py -l localhost:5001
The above command enables SpiderFoot to be accessible from the browser. Open your browser and browse to the server hostname or IP address followed by port 5001.http://192.168.77.21:8080.
By default, SpiderFoot can be accessed without any authentication. So it is recommended to enable basic authentication. Run the commands below to add your username and password to the password file:
echo "admin:Your-Strong-Password" > passwd
Congratulations! You have successfully installed SpiderFoot. Thanks for using this tutorial for installing SpiderFoot on your Ubuntu 20.04 LTS Focal Fossa system. For additional help or useful information, we recommend you check the official SpiderFoot website.
[su_box title=”VPS Manage Service Offer” style=”bubbles” box_color=”#000000″ radius=”10″]If you don’t have time to do all of this stuff, or if this is not your area of expertise, we offer a service to do “VPS Manage Service Offer”, starting from $10 (Paypal payment). Please contact us to get the best deal![/su_box]

