How To Set Up ModSecurity with Apache on Ubuntu 22.04 LTS

In this tutorial, we will show you how to set up ModSecurity with Apache on Ubuntu 22.04 LTS. For those of you who didn’t know, ModSecurity also known as Modsec is a robust Open-source firewall application for Apache web servers. It functions through rule sets, which allow you to customize and configure your server security.
This article assumes you have at least basic knowledge of Linux, know how to use the shell, and most importantly, you host your site on your own VPS. The installation is quite simple and assumes you are running in the root account, if not you may need to add ‘sudo‘ to the commands to get root privileges. I will show you the step-by-step installation of the ModSecurity with Apache on Ubuntu 22.04 (Jammy Jellyfish). You can follow the same instructions for Ubuntu 18.04, 16.04, and any other Debian-based distribution like Linux Mint.
Prerequisites
- A server running one of the following operating systems: Ubuntu 22.04, 20.04, 18.04, and any other Debian-based distribution like Linux Mint.
- It’s recommended that you use a fresh OS install to prevent any potential issues.
- SSH access to the server (or just open Terminal if you’re on a desktop).
- A
non-root sudo useror access to theroot user. We recommend acting as anon-root sudo user, however, as you can harm your system if you’re not careful when acting as the root.
Set Up ModSecurity with Apache on Ubuntu 22.04
Step 1. First, make sure that all your system packages are up-to-date by running the following apt commands in the terminal.
sudo apt update sudo apt upgrade
Step 2. Installing ModSecurity with Apache on Ubuntu 22.04.
By default, ModSecurity is available on Ubuntu 22.04 base repository. Now run the following command below to install the latest version of ModSecurity to your system:
sudo apt install libapache2-mod-security2
Then, enable the module and restart your Apache2 service to affect the new module and changes:
sudo a2enmod security2 sudo systemctl restart apache2
For additional resources on installing Apache, read the post below:
Step 3. Configuring ModSecurity.
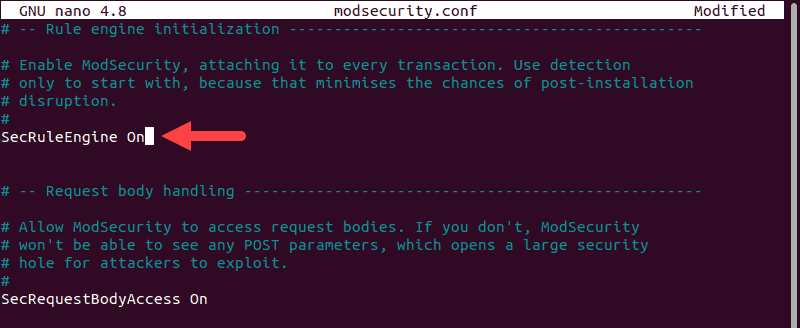
ModSecurity is set to log events according to default rules. You’ll need to edit the configuration file to adjust the rules to detect and block traffic:
sudo cp /etc/modsecurity/modsecurity.conf-recommended /etc/modsecurity/modsecurity.conf
Next, edit the file that you have copied using your favorite editor:
sudo nano /etc/modsecurity/modsecurity.conf
Change the value of SecRuleEngine from Detection Only to On:
SecRuleEngine On
Save and close the file, then restart Apache for the change to take effect:
sudo systemctl restart apache2
Step 4. Install Latest OWASP ModSecurity Rules.
Now we download the latest ModSecurity Core Rule Set (CRS) from the Open Web Application Security Project (OWASP):
wget https://github.com/coreruleset/coreruleset/archive/refs/tags/v3.3.2.zip
Next, extract the downloaded file:
unzip v3.3.2.zip.zip
Move the CRS setup file from the new directory into your ModSecurity directory:
mv coreruleset-3.3.2/crs-setup.conf.example /etc/modsecurity/crs-setup.conf
After that, we edit your Apache security2.conf file to ensure it’ll load ModSecurity rules:
nano /etc/apache2/mods-enabled/security2.conf
Add the following two lines at the end:
IncludeOptional /etc/modsecurity/*.conf Include /etc/modsecurity/rules/*.conf
Save and close the file, then restart Apache for the change to take effect:
sudo systemctl restart apache2
Step 4. Test ModSecurity Configuration.
Now we edit the default Apache configuration file and add two additional directives, using the default configuration as an example:
sudo nano /etc/apache2/sites-available/000-default.conf
Add the following file:
<VirtualHost *:80>
ServerAdmin webmaster@localhost
DocumentRoot /var/www/html
ErrorLog ${APACHE_LOG_DIR}/error.log
CustomLog ${APACHE_LOG_DIR}/access.log combined
SecRuleEngine On
SecRule ARGS:modsecparam "@contains test" "id:4321,deny,status:403,msg:'ModSecurity test rule has triggered'"
</VirtualHost>
Save and close the file, then restart Apache for the change to take effect:
sudo systemctl restart apache2
Finally, enter the following command below:
curl localhost/index.html?modsecparam=test
The response code should be 403. There should be a message in the logs that shows the defined ModSecurity rule worked.
Congratulations! You have successfully installed ModSecurity with Apache. Thanks for using this tutorial for installing the ModSecurity with Apache on Ubuntu 22.04 LTS Jammy Jellyfish system. For additional help or useful information, we recommend you check the official ModSecurity website.